Adobe Community
Adobe Community
- Home
- Acrobat Reader
- Discussions
- How to include PDF signature's embedded timestamp ...
- How to include PDF signature's embedded timestamp ...
How to include PDF signature's embedded timestamp authority chain revocation info in Adobe's RevInfo
Copy link to clipboard
Copied
Hello there,
I'm trying to create a LTV Enabled PDF Signature.
So far I was able to make Adobe Reader display the "Signature is LTV enabled" message following these steps:
- Retrieve revocation info (both CRLs and OCSP Responses, except for root certificates of course) for the signing certificate's full chain and for the timestamp authority certificate's full chain (used to add the signature's timestamp in step #4)
- Include revocation info retrieved in step #1 as a signed attribute for the signature to be computed in Adobe OID "1.2.840.113583" format:
adbe-revocationInfoArchival OBJECT IDENTIFIER ::= { adbe(1.2.840.113583) acrobat(1) security(1) 8 }
RevocationInfoArchival ::= SEQUENCE {
crl [0] EXPLICIT SEQUENCE of CRLs OPTIONAL,
ocsp [1] EXPLICIT SEQUENCE of OCSP Responses OPTIONAL,
otherRevInfo [2] EXPLICIT SEQUENCE of OtherRevInfo OPTIONAL }
OhterRevInfo ::= SEQUENCE {
Type OBJECT IDENTIFIER
ValValue OCTET STRING
}
- Perform the signature
- Embed a qualified timestamp in the signature generated in the step #3
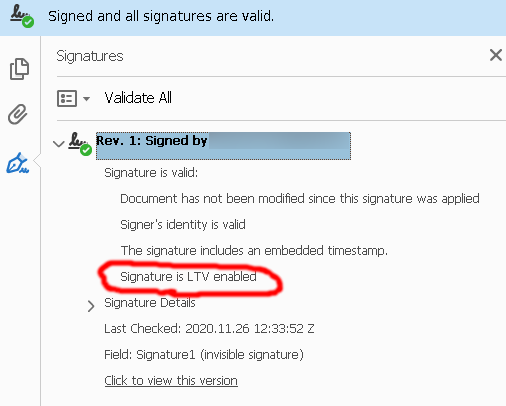
The previous steps' output gives me the "LTV Enabled" status in Adobe Reader:
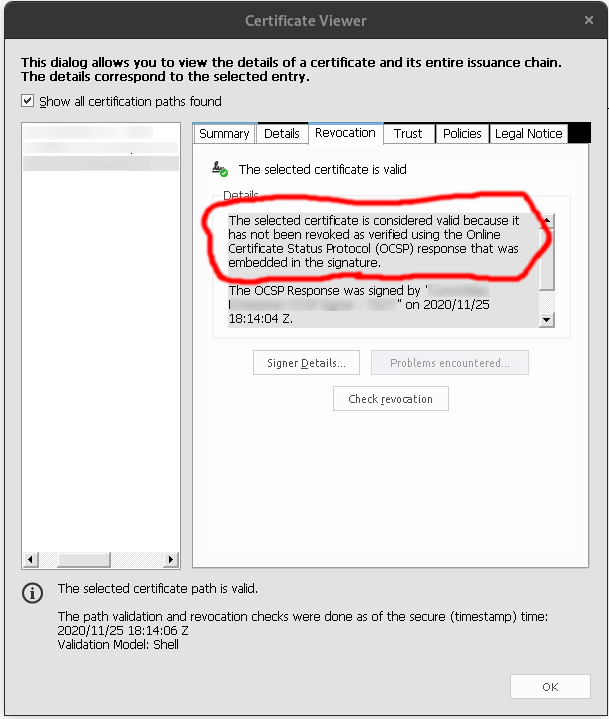
When I check which data Adobe Reader used to validate the certificate chain validity it presents the expected "The selected certificate is considered valid because it has not been revoked as verified using the Online Certificate Status Protocol (OCSP) response that was embedded in the signature."
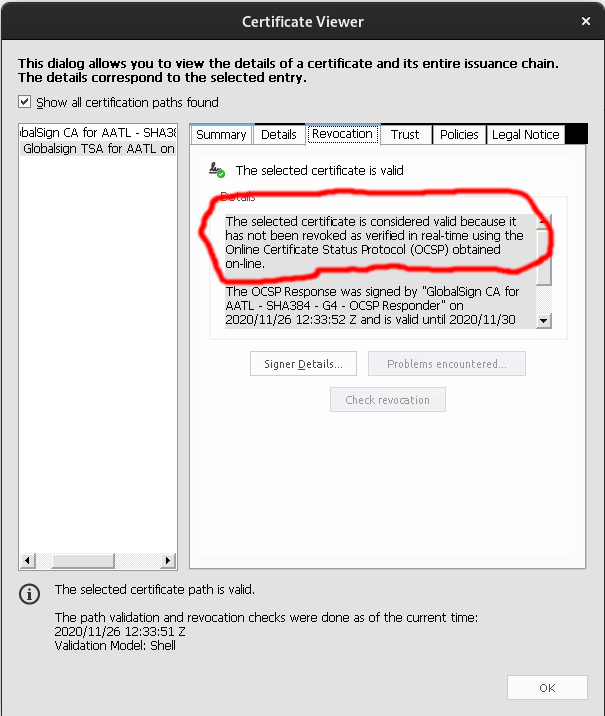
However, when I perform the same check for the Timestamp Authority's certificate chain it presents "The selected certificate is considered valid because it has not been revoked as verified in real-time using the Online Certificate Status Protocol (OCSP) obtained on-line."
The Signer's chain embedded CRLs/OCSPs are successfully used but the embedded TSA's chain CRLs/OCSPs are not.
**This begs some questions that need to be answered:**
- Why are not the TSA embedded CRLs/OCSPs embedded used?
- Do I have to place them elsewhere? If so, where?
- Or do I have to ask the Timestamping authority to return the CRLs and/or OCSP responses as signed attribute within the timestamp token?
Have something to add?