 Adobe Community
Adobe Community
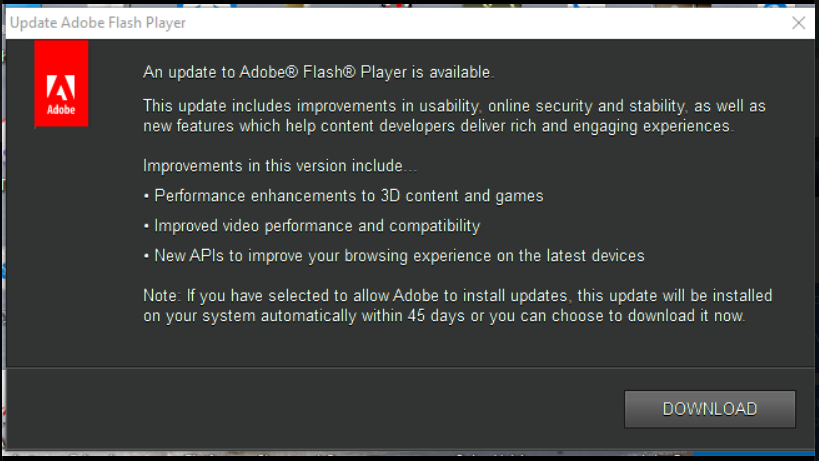
Adobe Update (Malware)
Copy link to clipboard
Copied
Hi, could somebody help me to remove the following (see below) This message loads when my laptop starts. After clicking download the malware install number of malicious software, corrupts browser and and makes the laptop "unusable". Antivirus (AVG does not removes the malware)
I am using windows 10
Copy link to clipboard
Copied
If you get this message when you start the system (BEFORE RUNNING THE BROWSER) then the app is already on your system, and if there is a virus you already have it. But this does look like the normal thing.
There is also a special kind of virus attack called "DNS poisoning" where the bad guys change the way your computer finds adobe.com and gets in there themselves. But this is pretty rare (and happens outside your computer).
So, what is this malware, and the bad effects. Please describe them in detail.
Copy link to clipboard
Copied
Hi, yes the “malware” is already installed. When the download button is clicked mu browser would be hijacked, the adware would float my laptop.As long as i do not press download, the software stays dormant
Avg or Windows Defender do not recognize it as “malware”
Thank you,
Copy link to clipboard
Copied
try spyhunter maybe you'll get more results
Copy link to clipboard
Copied
Thank you Robert, i will try and will post the results
a
Copy link to clipboard
Copied
I had the misfortune of inadvertently clicking on this assuming that it was a regular Adobe update... BIG Mistake!!!!
It has wrecked my 8-months work deleted critical files and destroyed their position on the file manager.
Norton could not catch or block it and even a subsequent forensic by them failed any trace.
I wonder if there were any measures from Adobe warning that such a thing existed.
I have learnt at a huge cost and want to take this warning as far and wide as I can.
it has also designated itself as a system hardware "To be protected" which is really creepy.
Stay Safe and spread the word far and wide.
Copy link to clipboard
Copied
Hi kunalm64662865,
Thanks for reporting the issue. If you know from which site you downloaded the malicious installer, please report it it phishing@adobe.com or private message me the same so that I can forward it to the phishing department.
Thanks!
Copy link to clipboard
Copied
I did not go looking for this update, it came as a pop-up on my PC.
Copy link to clipboard
Copied
What can you tell us about this "malware" except that it's malware? Names, symptoms etc.? How do you know it's malware when your antivirus does not? Please be detailed.
If it installs when you click Download, how are you getting rid of it to test this?
Copy link to clipboard
Copied
Sorry this happened to you. I'm going to leave some advice here for other folks that may run across this.
Unfortunately, because Flash Player is installed on billions of computers, it's a common target for impersonation for people distributing malware.
As an industry, we've done a pretty good job of defending against technical attacks that allow bad guys to install software without your authorization. In 2018, it's really difficult to do (assuming you're running a modern operating system and not something from 2005, in which case, you should get on that).
The result is that human factors are now the path of least resistance. It's easier to trick you into installing something on behalf of the attacker, vs. figuring out how to defeat all of the security stuff required to do it without your express permission.
In general, you're better off setting everything to update automatically. You can then go through life assuming that any update notifications you get are bogus. This is actually what we strongly recommend, and it generally applies to anything tasked with handing untrusted communication (the operating system, your web browser, flash player, etc.). The inconvenience of something functional breaking because of an update pales in comparison to the pain of recovering from identity theft.
Here are a few guidelines that will minimize your risk of getting tricked into installing malware:
- Wherever possible, use your operating system's App Store for downloading and updating software
- When software you want (like Flash Player) isn't available from the App Store for your operating system, always navigate directly to the vendor's website. If you need to search for the download, that's cool -- but avoid "download" sites, and find the vendor's actual download link
- Never download stuff from a link in an email or update dialog. Type it in. It's easy to disguise fake URLs in links using internationalized characters and things (e is not the same as è, but it might be really easy to miss if you're not looking closely). If it's a link from a URL shortener service like tinyurl.com/abcde or bit.ly/abcde, you don't know what the end result is going to be, and you're probably wise to just head to Google to find what you need instead.
- When the software offers automatic updates, just turn them on and stop worrying about maintaining all the moving parts running on your computer. The threat landscape is so much different than it was 10-15 years ago. Enable updates so that you're getting critical patches as soon as they become available. Be confident that any subsequent update notifications are probably fake, and act accordingly (either ignore them, or consult the vendor for guidance before doing anything).
For Flash Player specifically:
Always download Flash Player from here: https://get.adobe.com/flashplayer/
When you install, choose the default option of "Allow Adobe to Install Updates (recommended)", and we'll keep it updated for you.
Google Chrome ships Flash Player as a built-in component, and keeps it updated automatically. There's nothing separate to download, install or configure.
Microsoft Edge and Internet Explorer on Windows 8 and higher also include Flash Player as a built-in component of their browser, and updates are handled automatically through Windows Update. Again, as long as Windows Update is enabled, there's nothing to download or configure.
Also, while you've attempted to clean up the stuff that you can see, you installed malware on your machine. There's a large universe of unknown unknowns, but the malware guys at this point are generally professionals. They test against the popular antivirus and cleanup tools. While you may have removed the obvious visible signs of the malware infection, you're putting a lot of faith into the tools that you used. This sort of requires a gut-check on your part about what your risk tolerance and confidence level is. It also depends on what you do with the computer (health care, banking, etc.). Good malware is going to first establish a foothold, but the second order of business would be to ensure resilience. Without an exhaustive (and expensive) forensic analysis, there are no guarantees that you've eradicated everything that was installed.
If it were me, I'd probably back up all of the critical data on the machine and then burn the whole thing down and start from scratch (e.g. format the hard disk, reinstall the operating system and applications from pristine sources, install a reputable antivirus utility, scan my backups and then restore them.
I'd then go buy a password manager like LastPass/OnePass/KeyPass/etc. and set about ensuring that I have unique, strong passwords for each of the important online services that I use (including any email services that could be used to reset those passwords), and set up two-factor authentication wherever it's offered.
Copy link to clipboard
Copied
Thank you,
Copy link to clipboard
Copied
The only safe thing to do is wipe your disk, reinstall system, and restore the last backup taken before the infection.
Copy link to clipboard
Copied
Still, the popup will have come from a web site, even if it disguised itself as an ordinary window.
Copy link to clipboard
Copied
Given the age of this thread, and the fact that it's attracting spammy comments, I'm going to lock it. Please see my post (6, above) for advice and an explanation.